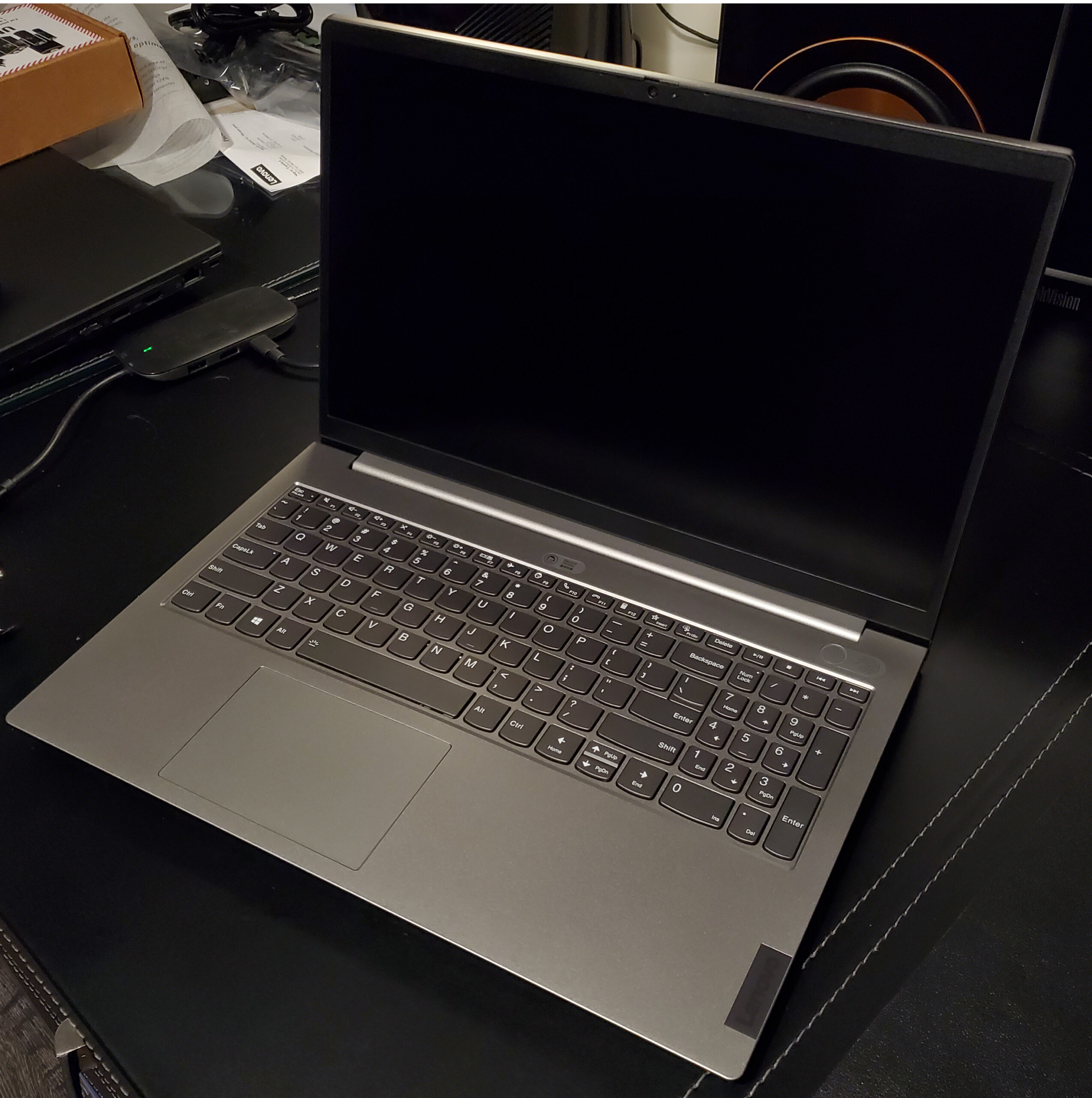
2022-07-04 ThinkBook 14 G2 ARE - ThinkBook 15 G2 ARE
Summary of changes ================== General Information: version FACN32WW 1. Optimize the setup menu information. 2. Enhancement to address Security vulnerability - LEN-77637 3. Enhancement to address Security vulnerability: CVE-2020-12944 : Insufficient validation of BIOS image length by ASP Firmware could lead to arbitrary code execution. CVE-2020-12946 : Insufficient input validation in ASP firmware for discrete TPM commands could allow a potential loss of integrity and denial of service. CVE-2020-12951 : Race condition in ASP firmware could allow less privileged x86 code to perform ASP SMM (System Management Mode) operations. CVE-2021-26312 : Failure to flush the Translation Lookaside Buffer (TLB) of the I/O memory management unit (IOMMU) may lead an IO device to write to memory it should not be able to access, resulting in a potential loss of integrity. CVE-2021-26361 : A malicious or compromised User Application (UApp) or AGESA Boot Loader (ABL) could be used by an attacker to exfiltrate arbitrary memory from the ASP stage 2 bootloader potentially leading to information disclosure. CVE-2021-26362 : A malicious or compromised UApp or ABL may be used by an attacker to issue a malformed system call which results in mapping sensitive System Management Network (SMN) registers leading to a loss of integrity and availability. CVE-2021-26363 : A malicious or compromised UApp or ABL could potentially change the value that the ASP uses for its reserved DRAM, to one outside of the fenced area, potentially leading to data exposure. CVE-2021-26366 : An attacker, who gained elevated privileges via some other vulnerability, may be able to read data from Boot ROM resulting in a loss of system integrity. CVE-2021-26368 : Insufficient check of the process type in Trusted OS (TOS) may allow an attacker with privileges to enable a lesser privileged process to unmap memory owned by a higher privileged process resulting in a denial of service. CVE-2021-26369 : A malicious or compromised UApp or ABL may be used by an attacker to send a malformed system call to the bootloader, resulting in out-of-bounds memory accesses. CVE-2021-26373 : Insufficient bound checks in the System Management Unit (SMU) may result in a system voltage malfunction that could result in denial of resources and/or possibly denial of service. CVE-2021-26376 : Insufficient checks in System Management Unit (SMU) FeatureConfig may result in reenabling features potentially resulting in denial of resources and/or denial of service. CVE-2021-26386 : A malicious or compromised UApp or ABL may be used by an attacker to issue a malformed system call to the Stage 2 Bootloader potentially leading to corrupt memory and code execution. CVE-2021-26388 : ** RESERVED ** CVE-2021-26382 : ** RESERVED ** This candidate has been reserved by an organization or individual that will use it when announcing a new security problem. When the candidate has been publicized, the details for this candidate will be provided. CVE-2021-26317 : Failure to verify the protocol in SMM may allow an attacker to control the protocol and modify SPI flash resulting in a potential arbitrary code execution. CVE-2021-39298 : A potential vulnerability in AMD System Management Mode (SMM) interrupt handler may allow an attacker with high privileges to access the SMM resulting in arbitrary code execution which could be used by malicious actors to bypass security mechanisms provided in the UEFI firmware.